In today's digital age, our identities are increasingly displayed online. This extensive digital footprint can make us exposed to identity theft and fraud. Fortunately, there are several steps you can take to protect your online persona and minimize the risk of becoming a victim.
One crucial step is to create strong, distinct passwords for all your accounts. Avoid using common passwords or repeating the same password across multiple platforms. Instead, employ a combination of symbols and numbers, and consider using a password manager to help you develop complex passwords that are easy to remember.
- Continuously review your bank accounts and credit card statements for any suspicious transactions.
- Remain vigilant when sharing personal details online, especially on social media platforms. Avoid posting private data like your full name, address, or birth date publicly.
- Enable two-factor authentication whenever possible to add an extra layer of security to your accounts. This requires you to enter a passphrase from your phone or email in addition to your password.
By following these simple strategies, you can significantly minimize the risk of becoming a victim of identity theft and protect your digital persona. Stay informed about the latest online threats and best practices to ensure your safety in the digital world.
Venturing the Labyrinth: Understanding copyright Laws and Their Implications
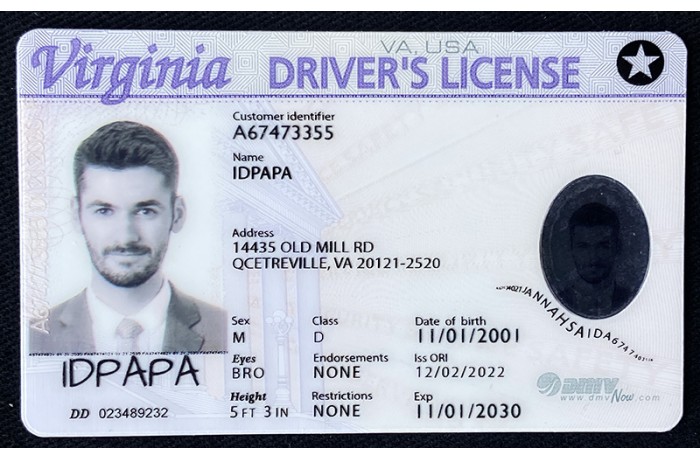
In the labyrinthine world of legal ramifications, fake identification presents a particularly complex challenge. Regulations surrounding copyright IDs vary significantly from jurisdiction to jurisdiction, making it crucial for individuals to inform themselves with the specific restrictions in their area. A seemingly innocuous act of producing a false ID can result in severe consequences, including monetary penalties and even imprisonment.
- Moreover, the implications of copyright use extend beyond legal ramifications. Possessing or employing a copyright ID can damage an individual's credibility and impede their future chances.
- Therefore, it is imperative for individuals to demonstrate caution and comply with all applicable laws and regulations. Acknowledging the gravity of copyright offenses can help mitigate the risk of unexpected consequences.
Biometric Authentication: The Next Frontier in Security
As technology advances, so too do the methods employed by malicious actors to compromise our digital protection. Traditional passwords, once considered robust, are increasingly susceptible to attacks. This presents a pressing need for more secure authentication methods. Biometric security emerges as a compelling solution, offering a level of personalization that transcends the limitations of typical passwords.
Biometrics leverage our unique physical traits for authentication. Fingerprint scanning, facial recognition, and iris analysis are just a few examples. These technologies offer several advantages over passwords, including enhanced accuracy, reduced risk of phishing, and increased user simplicity.
While biometric security presents a promising future, it's essential to address concerns surrounding privacy and information protection. Robust regulations and ethical guidelines are crucial to ensure responsible implementation. As we move towards a more interdependent world, embracing biometrics can pave the way for a more secure and reliable digital experience.
Authentication Solutions : Building Trust in the Digital Age
In today's increasingly interconnected world, establishing trust is paramount vital. As we interact in more and more online transactions and interactions, ensuring the validity of individuals Financial fraud and fake IDs becomes fundamental. Identity verification technology plays a pivotal role in bridging this trust gap.
Through advanced techniques, these solutions can verify user identities with high accuracy, mitigating the risks associated with impersonation. This not only safeguards sensitive information but also fosters a more secure and reliable digital environment.
From online banking and e-commerce to social media platforms and government services, identity verification is becoming an indispensable system for building trust and defending our digital identities.
Combatting Identity Theft: Leveraging Advanced Verification Solutions
In today's digital landscape, identity theft poses a significant threat to individuals and organizations alike. To combat this growing menace, sophisticated verification solutions are becoming increasingly crucial. These innovative technologies leverage multi-factor authentication to authenticate user identities with heightened accuracy and security. By implementing such robust verification measures, businesses can effectively mitigate the risk of identity theft, protect sensitive data, and build trust with their customers.
- One key advantage of advanced verification solutions is their ability to provide a frictionless experience for legitimate users while effectively deterring fraudsters.
- By integrating these technologies into existing systems, organizations can strengthen their overall security posture and limit the potential damage caused by identity theft incidents.
As technology continues to evolve, so too will the methods used by criminals to perpetrate identity theft. Therefore, it is essential for businesses to remain at the forefront of security innovation and adopt up-to-date verification solutions to safeguard their assets and reputation.
Protecting Your Privacy: Staying Ahead before ID Fraudsters
In today's increasingly digital world, safeguarding your personal information is more crucial than ever. Identity fraudsters are becoming highly skilled in their tactics, making it essential to stay one step ahead.
- Implement strong passwords and multi-factor authentication to protect your accounts.
- Be cautious concerning sharing sensitive data online or over the phone.
- Monitor your financial statements regularly for any suspicious activity.
- Shred documents containing personal information before discarding them.
- Consider placing a fraud alert on your credit report to limit access to your information.